Tpn Assessment: Master the tpn assessment in 5 Steps
- Feb 7
- 17 min read
Think of a Trusted Partner Network (TPN) assessment as the media industry’s seal of approval. It’s the official audit that proves your business can be trusted to handle high-value content from the world’s biggest studios. This isn't just a simple check-up; it's a deep dive into your security controls—everything from physical access at your facility to your digital networks—to ensure they meet the tough standards set by the Motion Picture Association (MPA).
Getting this wrong isn't just a compliance headache. Failing a TPN assessment, or not having one at all, can mean missing out on massive contracts with global players like Disney, Netflix, and Amazon Studios.
Why a TPN Assessment Is a Must-Have for Media Businesses

In the high-stakes game of film and television, content is everything. A pre-release leak of a blockbuster movie or a new streaming series can cost millions in lost revenue and seriously damage a studio's reputation. To combat this, the MPA created the Trusted Partner Network to establish a single, central security standard for the entire media supply chain. This move brilliantly eliminated the need for every studio to run its own separate, time-consuming, and expensive audits.
This unified approach brings some much-needed clarity and efficiency to the industry. Instead of drowning in different security questionnaires and audit teams, vendors can now go through one TPN assessment to prove their security game to all participating content owners. For any business touching the media lifecycle—from a small sound mixing studio to a massive visual effects house—TPN compliance has become non-negotiable for winning and keeping work.
Getting to Grips with the TPN Mission and MPA Standards
At its heart, the TPN's mission is simple: protect pre-release content from being stolen or leaked. It does this by assessing vendors against the MPA Content Security Best Practices, a super-detailed framework that covers every imaginable aspect of security. We're not just talking about firewalls and antivirus software here; the assessment goes deep into your daily operations, physical security, and management systems.
The framework is built to tackle real-world threats. By analysing past security breaches and vulnerabilities, the MPA identified recurring weak spots across the industry, like missing multi-factor authentication, sloppy vulnerability management, and poor physical controls. The guidelines directly address these gaps, forcing vendors to build a much stronger security foundation. If you're looking to understand the core principles behind these evaluations, this practical guide to compliance and risk assessment is a great place to start.
Who Needs to Get Assessed?
If your company handles sensitive or pre-release media content in any form, a TPN assessment is almost certainly in your future. This applies to a huge range of service providers across the media and entertainment world, including:
Post-production houses that manage editing, colour grading, and sound design.
Visual effects (VFX) studios that create digital assets and animations.
Dubbing and subtitling services that localise content for global markets.
Marketing and distribution partners involved in making trailers and promotional material.
Digital asset management (DAM) providers that store and manage media files.
Key Takeaway: A TPN assessment is more than an IT audit. It’s a full-on business evaluation that shows you can be a trusted guardian of a client's most valuable intellectual property. Without it, you’re practically invisible to the major studios.
The Different Tiers of TPN Assurance
The TPN uses different "Shields" to show varying levels of security assurance, helping content owners make smart, risk-based decisions about their partners. While a self-assessment is a decent first step, the big studios almost always demand a higher level of validation from their key vendors.
The two main tiers you'll come across are the Blue Shield and the Gold Shield. The Blue Shield is earned through a detailed, self-reported questionnaire. The Gold Shield, on the other hand, requires a formal, independent audit carried out by a TPN-accredited assessor who validates your security controls either on-site or remotely. For a closer look at what this involves, our article on how to unlock TPN certification to partner with Disney and Netflix has you covered. This intense validation process is precisely why the Gold Shield has become the industry benchmark for working on top-tier projects.
Mastering The Core Security Controls
To get through a TPN assessment, you need to forget theory and get practical. What really matters are the specific security controls assessors will be looking at, which are all laid out in the MPA Content Security Best Practices. This document is your playbook for protecting high-value content, and it's essential you know it inside and out.
The assessment isn’t about who has the flashiest, most expensive tech. It’s about proving you have consistent, well-documented, and effective security practices woven into every part of your operation. Assessors have a knack for spotting the difference between what your policies claim and what your teams are actually doing.
Digital Defences and Access Management
Your digital infrastructure is your first line of defence, and it's where assessors start digging. They’ll pay close attention to how you manage access and, crucially, how you segment your network to stop threats from moving around. A flat network, where a front desk computer could potentially talk to a server holding pre-release content, is a massive red flag they'll spot a mile away.
One of the most important concepts here is the principle of least privilege. All it means is that every user and every system should only have the bare minimum access needed to do their job. Nothing more. For instance, a sound mixer has absolutely no business accessing visual effects (VFX) files, and your systems must be configured to enforce that boundary.
Here are a few digital controls that are simply non-negotiable:
Multi-Factor Authentication (MFA): Every remote access point needs MFA, whether it's a VPN or a cloud-based review platform. This is one of the most common findings in assessments because time and again, a lack of MFA proves to be a critical weak spot.
Network Segmentation: Your production network must be completely isolated from your corporate or guest Wi-Fi networks. This simple step prevents a breach on a less secure network from ever reaching your most valuable assets.
Regular Vulnerability Scanning: It's not enough to just scan your systems for vulnerabilities. You need a documented process showing you do it regularly, and more importantly, a plan to patch what you find—fast.
When you're designing all this, a big decision that shapes your security controls is whether to go with On-Premise vs SaaS solutions. Each path comes with its own security responsibilities that you'll have to account for in your TPN assessment.
To help you get a clearer picture of what the TPN assessment covers, here's a quick look at the main security domains and what each one is trying to achieve.
| Key TPN Security Domains at a Glance | | :--- | :--- | :--- | | Security Domain | Core Objective | Example Control | | Governance & Risk Management | Establish a formal security structure and manage risks effectively. | Maintain an Information Security Management System (ISMS). | | Physical Security | Protect facilities, hardware, and sensitive areas from unauthorised access. | Use access control systems (key cards, biometrics) on server rooms. | | Infrastructure Security | Secure networks, servers, and endpoints against digital threats. | Implement network segmentation to isolate production environments. | | Content Security & Workflow | Protect content throughout its entire lifecycle, from ingest to delivery. | Enforce unique user accounts and the principle of least privilege. | | Access Control | Ensure only authorised individuals can access systems and data. | Require Multi-Factor Authentication (MFA) for all remote access. | | Incident Management | Detect, respond to, and recover from security incidents promptly. | Have a documented and tested Incident Response (IR) plan. | | Business Continuity | Ensure operations can continue and content is protected during a disruption. | Maintain and test a Disaster Recovery (DR) plan for critical systems. |
Understanding these domains is the first step, but the real work lies in implementing and documenting the specific controls within each one.
Physical Security in Sensitive Areas
While digital threats often steal the headlines, a TPN assessment puts just as much weight on physical security. Your most valuable content probably lives on servers and workstations right inside your building, which makes controlling physical access absolutely critical.
Be prepared for assessors to literally walk through your facility to see your controls in action. They’ll check for unlocked server rooms, watch to see if people tailgate through secure doors, and look for sensitive information visible on screens in open areas.
Real-World Scenario: An assessor might try to walk past your reception and into a secure area without an access card. A well-trained team will politely but firmly stop them and follow the visitor access procedure to the letter. This is a perfect demonstration of a strong security culture.
Here are some of the key physical security measures you'll be expected to have:
Access Control Systems: Use key cards, fobs, or biometrics for any sensitive area—that includes server rooms, edit suites, and even storage closets.
Detailed Access Logs: You must be able to pull logs showing exactly who went into sensitive areas and when. This is vital for any investigation if an incident occurs.
Surveillance: CCTV cameras should cover all entrances, exits, and sensitive locations. You’ll also need to retain the footage according to MPA guidelines.
Secure Hardware Handling: Have strict, documented procedures for managing physical media like hard drives. This means knowing where they are, keeping them securely stored, and sanitising them properly before disposal.
Incident Response and Business Continuity
Having strong defences is great, but you have to plan for the day they might fail. A documented and tested Incident Response (IR) plan is a mandatory requirement for any TPN assessment. This is more than just a technical checklist; it’s a business-level strategy that details exactly how you’ll react to a security breach.
The plan needs to spell out roles and responsibilities, how you'll communicate with clients and stakeholders, and the technical steps to contain and eliminate the threat. Crucially, you must be able to prove you've tested it, either with tabletop exercises or full-blown simulations. A plan that’s just sitting on a shelf has never been tested is worthless in an assessor’s eyes.
Likewise, your Business Continuity and Disaster Recovery (BCDR) plans show that you can keep operating and protect your clients' content during a major disruption, like a power outage or a natural disaster. For a deeper look at building out these security frameworks, check out our ultimate guide to cyber security for companies in NZ.
Getting a solid handle on these core controls is what turns a TPN assessment from a stressful audit into a valuable process for proving and improving your security.
Your TPN Assessment Preparation Playbook
Alright, moving from theory to practice is where the real work of a TPN assessment kicks off. A structured, methodical approach is your best friend here—it can turn what feels like a daunting audit into a manageable project, swapping chaos for confidence. This playbook gives you a clear path to get your organisation sorted before an assessor even walks through the door.
The very first move? Get the right people in the room. This isn't just an "IT problem." A TPN assessment is a business-wide responsibility that needs input from across the board. Trying to tackle it in a silo is a guaranteed recipe for missed deadlines and overlooked details.
Assemble Your Internal A-Team
Your TPN assessment team should be a cross-functional group of people who get both the technical controls and the day-to-day operational workflows. This is the only way to get a complete, honest picture of your security posture, not just a theoretical one.
Your core team absolutely needs to include people who can speak to:
IT and Security: This is your technical lead, the person responsible for network diagrams, firewall rules, access logs, and vulnerability management.
Operations and Production: These are the folks who manage the content lifecycle. They know exactly how files are ingested, moved, and delivered, providing crucial context for your workflow documentation.
Facilities Management: This person owns physical security—think access card systems, CCTV footage, and visitor protocols.
Human Resources: HR is key for managing employee onboarding and offboarding, security awareness training records, and policy acknowledgements.
Senior Leadership: Having a project sponsor from the leadership team is vital. They can secure resources, make final calls on tricky decisions, and drive accountability across the business.
Defining roles and responsibilities clearly from the very beginning saves a world of pain later. Everyone needs to know exactly what evidence they’re responsible for gathering and which security controls fall under their watch. It’s a simple step that can prevent countless hours of frantic scrambling down the line.
Conduct a Thorough Self-Assessment
Before you can fix your security gaps, you have to find them. A rigorous self-assessment against the MPA Content Security Best Practices is without a doubt the most critical phase of your preparation. This isn't a quick skim-through; it's a meticulous, line-by-line review of every control you have in place.
The goal is to honestly evaluate where you stand against every single requirement. Be critical and objective. If a policy exists on paper but isn't consistently enforced on the floor, that’s a gap. If a control is in place but you lack the documentation to prove it, that’s also a gap.
A common mistake we see is organisations assuming a control is working just because it was implemented years ago. A proper self-assessment forces you to verify everything, and it often reveals that processes have drifted or technology has become outdated.
This process essentially mimics what the official TPN assessor will do, giving you an invaluable preview of potential findings. It lets you document what you're doing well and, more importantly, create a prioritised list of weaknesses that need immediate attention.
The diagram below breaks down the core control areas your self-assessment will cover, hitting on access, physical security, and incident management.
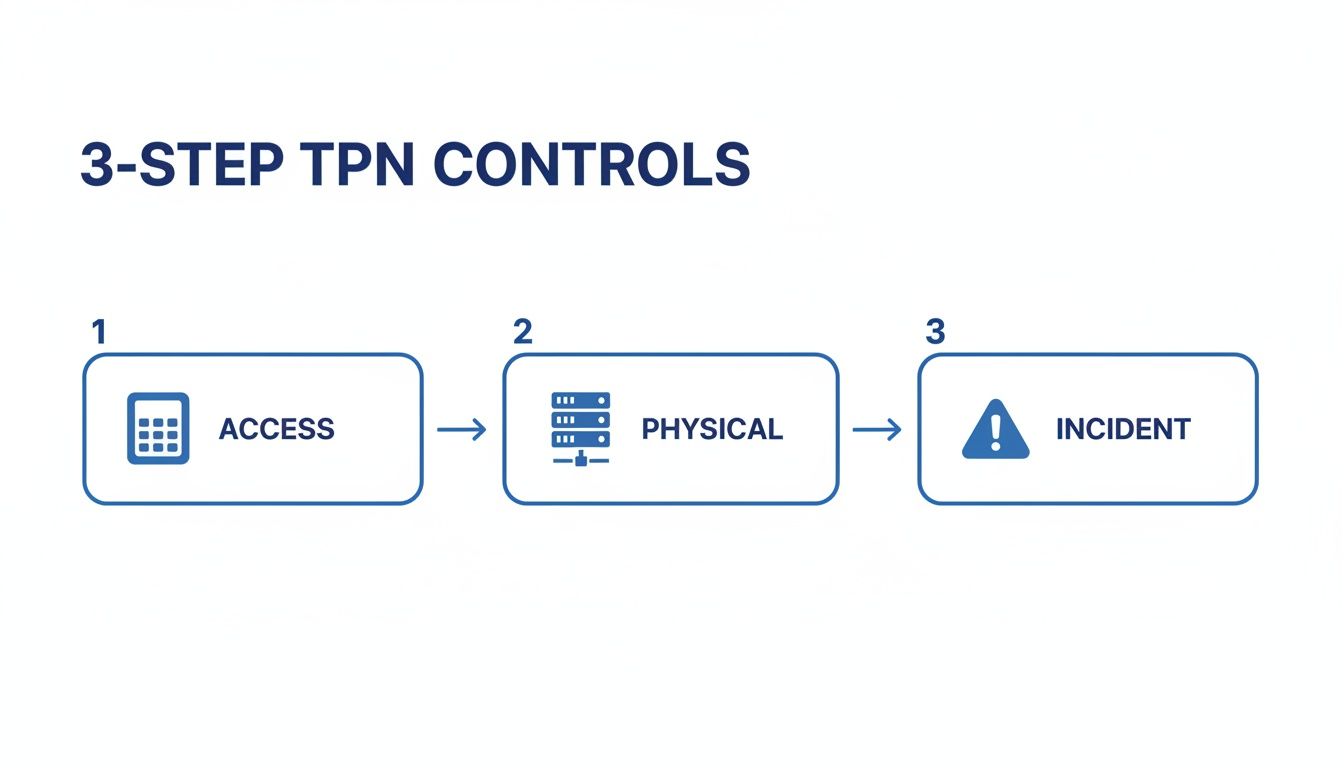
This flow highlights just how interconnected the TPN controls are, reinforcing the need for a unified strategy that spans digital, physical, and procedural security.
Create a Realistic Remediation Plan
Your self-assessment will inevitably uncover issues—that’s the whole point. The next step is to build a remediation plan, which is essentially a formal, documented project plan for fixing every single gap you've identified. This document becomes your roadmap to compliance.
A successful remediation plan is much more than a simple to-do list. It must be specific, actionable, and above all, realistic. For each finding from your self-assessment, your plan should detail:
The Specific Gap: Clearly describe the problem and which MPA control it relates to. For example, "Remote access via VPN does not enforce Multi-Factor Authentication (MFA)."
The Proposed Solution: Outline the technical or procedural changes needed to close the gap. For instance, "Implement a new MFA solution and integrate it with the existing VPN."
The Owner: Assign a specific individual from your A-team who is responsible for seeing the fix through to completion. Accountability is key.
The Timeline: Set a realistic deadline. Be honest about dependencies and resource availability to avoid setting your team up for failure.
The Evidence: Define what documentation will be needed to prove the control is in place and effective, like configuration screenshots or updated policy documents.
Let’s walk through a real-world scenario. A post-production house discovers during their self-assessment that their production network isn't properly segmented from their corporate network. This is a major finding.
Their remediation plan would look something like this:
Remediation Task | Description | Owner | Deadline | Evidence |
|---|---|---|---|---|
Network Segmentation | Reconfigure network switches and firewalls to create a logically separate production VLAN. Restrict all traffic between the production and corporate networks, except for approved, monitored connections. | IT Manager | 4 Weeks | Updated network topology diagram, firewall rule set screenshots, and results from a successful penetration test verifying segmentation. |
This structured approach transforms a vague problem like "improve network security" into a concrete, measurable project with clear ownership. It ensures that by the time the official assessor arrives, you haven't just fixed your weaknesses—you also have all the organised evidence ready to prove it. This proactive strategy is the absolute foundation of a successful TPN assessment.
Organising Your Evidence for a Seamless Audit
When it comes to a TPN assessment, one simple truth trumps everything else: if you can't prove a control exists, it might as well not. Your security measures could be bulletproof, but an assessor has no way to validate them without clear, organised evidence. This is exactly where many businesses get tripped up, turning the final audit into a frantic scavenger hunt through shared drives and old email threads.
The trick is to treat evidence collection as a core part of your preparation from day one, not an afterthought. Every policy document, access log, and training record is a puzzle piece. When you assemble them correctly, they present a complete and confident picture of your security posture. A proactive approach here saves a massive amount of stress and dramatically improves your chances of a smooth assessment.
Building Your Centralised Evidence Locker
Forget trying to manage this process in spreadsheets or scattered folders. To stay organised, you need a single source of truth.
A centralised platform, like a customised board in monday.com, can transform evidence collection from chaotic to controlled. It allows you to create a dedicated space to track every documentation request, assign clear ownership, set deadlines, and attach files directly to the control they satisfy.
Picture a digital board where each row represents a specific MPA control. You can have columns to track the status (Not Started, In Progress, Ready for Review), the assigned owner from your A-team, and a due date. Most importantly, a file column lets you attach the evidence—like a PDF of your Incident Response Plan or a screenshot of MFA settings—directly to the relevant control.
This gives you total visibility. At any moment, your project lead can see exactly how far along you are, who might be falling behind, and where potential roadblocks are forming. It completely eliminates that last-minute panic of trying to find a network diagram you thought was finished weeks ago.
The Essential Evidence You'll Need to Hand Over
While the specific documentation will vary based on your operations, some pieces of evidence are almost universally required in a TPN assessment. Having these prepared, polished, and ready to go is non-negotiable.
Here are some real-world examples of what assessors will ask for:
Network Topology Diagram: A clear, current diagram showing how your network is structured. It must visually demonstrate the segmentation between your production, corporate, and guest networks.
Employee Security Training Records: Proof that all staff, including contractors, have completed mandatory security awareness training. This could be a report exported from your learning management system or a simple signed register.
Vulnerability Scan Reports: Recent, dated reports from your vulnerability scanning tools. Crucially, you’ll also need to show evidence of how you have remediated or mitigated any critical findings.
Access Control Logs: System-generated logs from key card or biometric systems for sensitive areas like server rooms. These must show clear timestamps and user identification for every entry.
The power of a structured, evidence-based process isn’t unique to media security. For instance, a six-year study at Auckland City Hospital found that implementing a specialist nurse to oversee total parenteral nutrition (TPN) significantly improved patient outcomes. The prospective collection of data on 498 TPN episodes across 484 patients showed how organised tracking and documentation enhance safety. This really underscores the value of digitised workflows for managing compliance, whether in healthcare or media.
A Real-World Evidence Management Scenario
Let's see how this works in practice. Imagine a VFX studio is prepping for its Gold Shield audit. Using their monday.com board, the IT Manager is assigned the task: "Provide Evidence of MFA on Remote Access."
The task is created and linked directly to the relevant MPA control for remote access security.
The IT Manager takes screenshots of the VPN configuration settings, clearly showing that MFA is enabled and required for all users. They also export the company policy document that mandates its use.
Both the screenshots and the policy document are uploaded straight to the task on the board.
The IT Manager updates the task status to "Ready for Review."
The project lead gets a notification, reviews the attached evidence to ensure it's clear and sufficient, and marks the task as "Complete."
This simple workflow creates an organised, auditable trail. When the TPN assessor asks for proof of MFA, the studio can pull up the exact documentation instantly, without breaking a sweat. For organisations looking to implement these kinds of secure, localised workflows, it's also worth exploring how solutions like Microsoft 365 in New Zealand can help secure local data residency.
Ultimately, this structured approach doesn't just pave the way for a smoother TPN assessment—it builds a stronger, more accountable security culture for the long run.
How Wisely Can Help You Nail Your TPN Compliance

Getting ready for a TPN assessment isn't just an IT project; it's a company-wide effort that touches on your technology, daily processes, and your people. It requires a fundamental shift in how your business thinks about and handles security.
We've seen plenty of organisations get bogged down trying to coordinate it all. That’s where Wisely comes in. We act as your strategic partner, pulling all these threads together under a clear methodology that guides you from that initial "Where do we start?" moment right through to a successful assessment and beyond.
Our whole approach is built on a proven plan-build-deliver framework. We don’t just hand over a checklist and wish you luck. Instead, we get in the trenches with your team to map out a practical, end-to-end strategy that actually fits your operational needs and budget. This makes the whole compliance journey feel less like a chore and more like a sustainable business improvement.
Plan and Build: Your Security Foundation
First things first, we need to know exactly where you stand. Our managed IT and cybersecurity experts kick things off with a thorough gap analysis, benchmarking your current setup against the MPA best practices. This isn't just a paper-based exercise; it's a hands-on review of your infrastructure, from how your network is configured to who can physically access your servers.
Based on what we find, we get to work building a robust and compliant technical foundation. This often means tackling a few key areas:
Secure Cloud Environments: We can design and implement cloud infrastructure that meets the stringent TPN requirements for things like data segregation and protection.
Robust Endpoint Protection: This involves deploying and managing advanced security tools across all your workstations to shut the door on malware and unauthorised access.
Network Segmentation: Re-architecting your network to isolate sensitive production environments from your corporate and guest networks. This is a non-negotiable TPN control.
This foundational work ensures that the technical controls required for your TPN assessment are not only in place but are configured correctly and managed for the long haul.
Deliver: Custom Workflows for Painless Compliance
Once the technical controls are solid, the next big hurdle is managing all the evidence and tracking every single remediation task. Honestly, this is where most teams get lost in spreadsheet hell.
This is where our expertise in business process automation, particularly with platforms like monday.com, gives you a massive advantage.
We design and build custom workflows specifically for managing TPN compliance. Imagine a single, centralised board that gives everyone real-time visibility into your preparation. You can track evidence collection for every control, assign remediation tasks to specific people with clear deadlines, and see your overall progress at a glance.
A structured approach to assessment and documentation is vital, no matter the industry. For instance, surveys in New Zealand neonatology units found significant variations in parenteral nutrition protocols. You can see how structured digital assessments improve collaboration on these complex processes by reading the findings from an Australian and New Zealand survey.
This completely eliminates the chaos of juggling endless spreadsheets and shared folders, creating one source of truth for your entire audit trail.
By partnering with Wisely, you’re not just preparing to pass an assessment. You’re building a more resilient, efficient, and secure way of working. It’s about turning a compliance headache into a genuine, lasting business improvement.
Your TPN Assessment Questions Answered
If you're gearing up for a TPN assessment for the first time, you've probably got a few questions. That's completely normal. Getting your head around the practicalities can make the entire process feel less daunting and helps you point your team in the right direction from day one.
Let's cut through the jargon and get straight to the real-world answers for the questions we hear most often from media and entertainment businesses.
How Long Does a TPN Assessment Take?
The honest answer? It really depends on where your security is at right now. The single biggest variable is the preparation phase—the time you spend on your own internal self-assessment and fixing any gaps you uncover. This can be anything from a few weeks to several months.
Once you’re confident you’re ready, the official assessment with a TPN-accredited assessor usually takes between two and five days, whether it's on-site or remote. After that, you’ll want to factor in another few weeks to get the final report back and formally address any findings. A solid project plan is your best friend here, keeping everything moving and on schedule.
What Is the Real Difference Between TPN Blue and Gold Shields?
Think of the TPN Blue Shield as your detailed, self-declared security statement. You're filling out a comprehensive questionnaire that measures your security controls against the MPA Best Practices. It’s a crucial first step and shows you’re serious about security, but it's not independently verified.
The TPN Gold Shield is the formal audit. A TPN-accredited, third-party assessor comes in (either in person or remotely) to validate that your security controls aren't just policies on a shelf—they're actually implemented and working effectively. For any high-value content, the major studios will almost always require their vendors to hold a Gold Shield. It's the highest level of assurance they can get.
What Are the Most Common Reasons for Failing a TPN Assessment?
Over the years, we've seen companies trip up on the same few things time and time again. Disorganised or incomplete documentation is a huge one. If you can't show an auditor the proof that a control exists, then for the purpose of the assessment, it doesn't. Another common pitfall is applying security policies inconsistently across different departments.
Other frequent failure points include:
Weak access controls: Not properly enforcing the "principle of least privilege," which means people have access to more data and systems than they actually need to do their jobs.
Poor physical security: Simple things like unlocked server room doors, a lack of visitor logs, or unsecured media storage can be an instant red flag.
No formal incident response plan: It's not enough to just have a plan for dealing with a security breach. You need to show that it’s documented, and just as importantly, that you’ve actually tested it.
The single best way to avoid these common mistakes is to be ruthless during your preparation. A truly honest and detailed self-assessment will uncover your weak spots, giving you a chance to fix them long before the official auditor walks through the door.
At Wisely, we guide you through every stage of your TPN assessment, from the initial gap analysis to building the custom workflows you need for a smooth audit. We blend managed IT and cybersecurity expertise with business process automation, turning a complex compliance exercise into a genuine, lasting improvement for your business. Find out how we can support your journey at https://www.wiselyglobal.tech.
Comments